Securing Flussonic¶
In this section you will learn how to limit access to the Flussonic Administration panel and the server.
Danger
If hackers get access to your Flussonic Administration UI, they will be able to read and modify any file on the disk.
Login and password¶
Flussonic allows you to set two types of access in config: view_auth and edit_auth.
view_auth user password;is used for access to readonly API Flussonic functions:
getting streams info, status and statistics.
edit_auth user password;is used for giving the full access to Flussonic.
Flussonic can store the password in a hashed format. We know that clients often forget their passwords and look them up in the config file, even when is is not stolen.
We recommend using this option if the server is used by a group of people and the company uses automated tools to track passwords that are stored unprotected.
Limiting access to Flussonic UI by IP addresses or ports¶
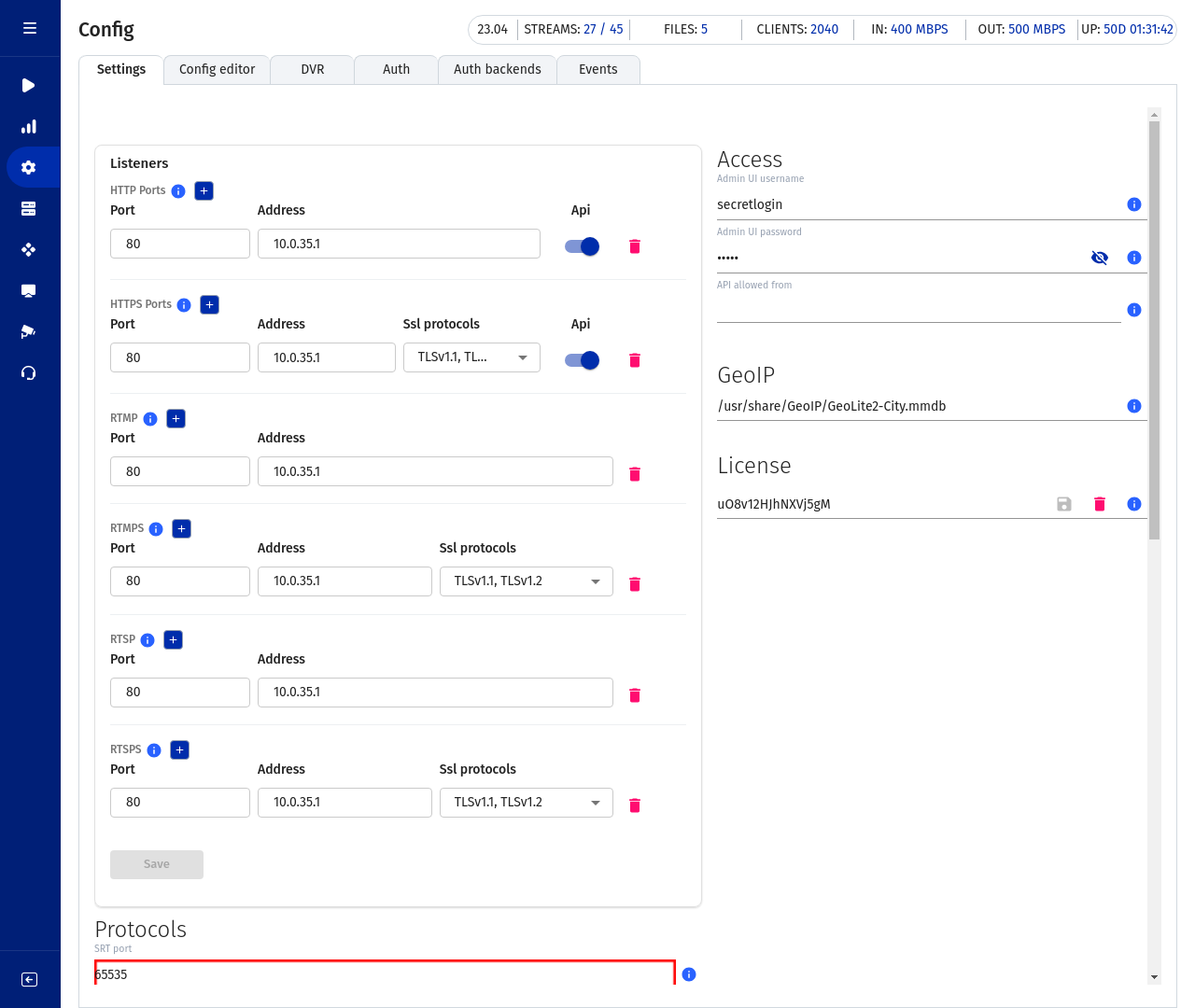
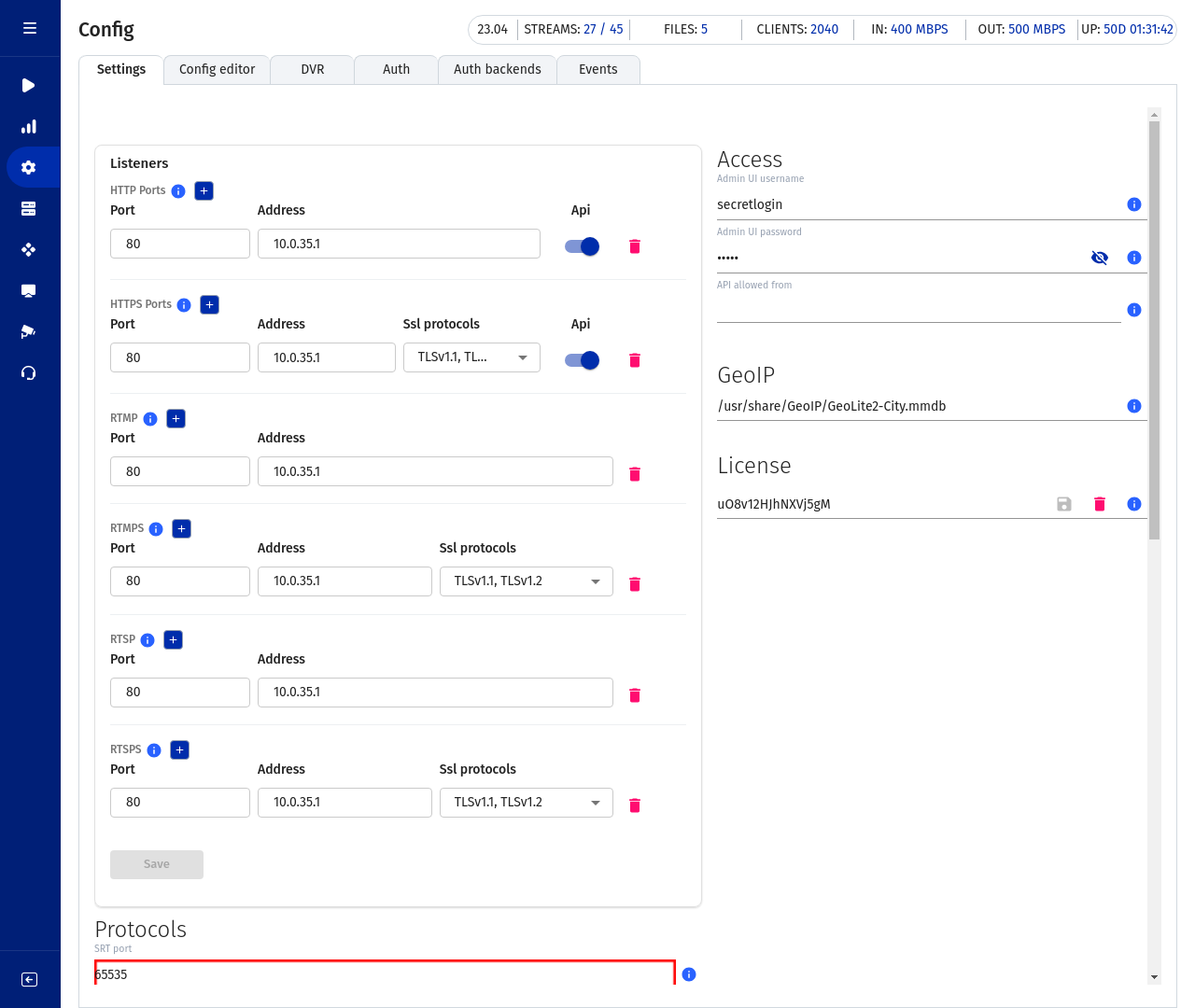
Access to Flussonic UI is restricted on "white list" basis, i.e. you should list all the ports where you want Flussonic UI available. For that, go to the Listeners section of the Config tab and specify ports for Flussonic to listen. You may leave the Address empty to allow all IP addresses or specify a value to allow requests by the specified IP only.
Optionally, for HTTPS, RTMPS, and RTSPS, you can select the version(s) of SSL protocols you wish to use on the specified IP and port. Clients not supporting these versions will be denied.
Warning
Be careful when changing the Address setting. Incorrect configuration may lead to Flussonic UI becoming unavailable from your computer, for example if you specify an IP address in local network while making configurations through the Internet. Make sure you have an alternative way to access the server in case of loss of access to UI, e.g. it is available physically or by SSH.
Limiting API calls by IP addresses or ports¶
By default, Flussonic processes API requests on all HTTP or HTTPS ports you specify in config.
You can configure listeners in Flussonic to forbid API calls on the specified port(s) in one of the following ways:
-
in Flussonic UI, go to the Listeners section of the Config tab to disable the API switch for IP addresses and ports where you do not want to accept API calls:
-
in the configuration file (
/etc/flussonic/flussonic.conf), addapi false;directive in the parameters of the IP address and port you wish to forbid for API calls:https 443 { api false; }
Uploading SSL certificates¶
If you already have an SSL certificate for Flussonic issued by a third-party provider or generated by yourself, you can upload it from your computer to the server through the Flussonic's web interface.
- First, specify the port for HTTPS. Open the UI and go to Config -> Settings -> Listeners and enter the port for HTTPS, for example, 443.
-
Then go to the TLS-tunneled protocols and click Upload certificates, choosing the certificate and the key files. Also the CA-certificate may be uploaded.

If you encounter an error when trying to upload your certificate, check that you have only one certificate in the file. As of now, Flussonic's UI does not support uploading files with anything (like root and/or intermediate certificate, key, etc.) except the certificate in them. Please use other means to add such certificates, for example send them over SSH.
Any SSL certificates used by Flussonic are stored in a single folder — /etc/flussonic or /etc/streamer (in a cluster installation). Flussonic will automatically rename files to streamer.crt, streamer-ca.crt, and streamer.key.
To remove the uploaded files related to a certificate, click a recycle bin icon in Config -> TLS-tunneled protocols next to the file list.
Generating SSL certificates¶
In order to switch the Administrator's web interface to HTTPS, you need to enable the port for HTTPS in the Flussonic configuration. Open the web interface and specify the port for HTTPS in Config -> Settings -> Listeners, for example, 443.
You can generate your own SSL certificate. Below are commands that you should run one by one to generate a Flussonic's own self-signed certificate. Each time the system prompts you to enter the password for the certificate, press Enter without typing anything.
cd /etc/flussonic
openssl genrsa -des3 -out streamer.key 1024
openssl req -new -key streamer.key -out streamer.csr
mv streamer.key streamer.key.org
openssl rsa -in streamer.key.org -out streamer.key
openssl x509 -req -days 365 -in streamer.csr -signkey streamer.key -out streamer.crt
Then put the resulting files to /etc/flussonic (/etc/flussonic/streamer.crt and /etc/flussonic/streamer.key). Alternatively, you can upload these files through the web interface. To do this, go to Config > SSL-tunneled protocols and click Upload certificates.
Intermediate and CA certificates will be taken from /etc/flussonic/streamer.crt.
For the most recent OpenSSL commands description, refer to the manual pages in the OpenSSL documentation.
Let's Encrypt certificates¶
Let's Encrypt is offering free SSL certificates with 1-month expiration since April 2016. The certificate is issued in automatic mode.
We have added the support for LetsEncrypt into Flussonic. How to setup LetsEncrypt
Protecting configuration file¶
You can prevent the configuration file from being modified via the API (web interface). JFor this you should create the file /etc/flussonic/flussonic.conf.locked by executing the following command:
touch /etc/flussonic/flussonic.conf.locked
With this file in place nobody will be able to change Flussonic settings via the web UI.
Running Flussonic as an unprivileged user¶
You can run Flussonic as an unprivileged user. Run the following commands:
adduser flussonic --home /var/lib/flussonic --disabled-password
chown -R flussonic /etc/flussonic/
chown -R flussonic /var/lib/flussonic/
chown -R flussonic /var/run/flussonic /var/log/flussonic /etc/flussonic/.erlang.cookie
setcap cap_net_bind_service=+ep /opt/flussonic/lib/erlang/erts-*/bin/x86_64-linux-gnu/beam.smp
Then create override systemd unit using systemctl edit flussonic command:
[Service]
User=flussonic
Group=flussonic
To make Flussonic run as 'root' again, empty override file.
Protecting video from viewing by the Administrator¶
By default, the users with Flussonic Administrator rights can play back any stream by using the Administration UI. The special Administrator's authorization token is used for that.
You may want to prohibit viewing some streams by the Administrator - streams protected by authorization.
To prevent the Flussonic Administrator from playing back any stream that needs authorization:
1) Edit Flussonic service unit file (/lib/systemd/system/flussonic.service) - do it by using the systemd's override mechanism.
systemctl edit flussonic
This command opens a text editor (nano by default).
2) Add these lines:
[Service]
Environment=STREAMER_ADMIN_VIEW_DISABLE=true
Press Ctrl-X, then Y to save and exit.
3) Restart Flussonic:
service flussonic restart
Now if a stream requires authorization, the player in the Flussonic UI will return a 403 error at the attempts to play the stream back with an Administrator's token.
Streams without configured authorization will be played back as usual.
Protecting the file system from access via the UI¶
In the Flussonic UI, the user (Administrator) sets paths to VOD, DVR, and cache. You can configure Flussonic to limit the user to certain directories, so that Flussonic will allow storing files only in that directories and subdirectories. For example, this allows you to protect the /root directory.
Flussonic checks the paths in vod vod, dvr, cache, copy, and in the schemas playlist:/// and sqlite:///.
To configure this, add the environment variable FLUSSONIC_DATAPATH and specify the uppermost directory allowed for creating VOD, DVR, cache and so on.
Warning
In order for Flussonic to restart successfully with the new settings, make sure the current configuration does not have paths to the directories located above the one specified in the FLUSSONIC_DATAPATH variable.
To add FLUSSONIC_DATAPATH, you can use the systemd's override mechanism:
systemctl edit flussonic
This command opens a text editor (nano by default).
Add directories in the following way:
[Service]
Environment=FLUSSONIC_DATAPATH=/storage:/mount:/copy
Press Ctrl-X, then Y and Enter to save and exit.
Restart Flussonic:
service flussonic restart
Users will be limited to /storage, /mount and /copy and their subdirectories.